Introduction
Enterprise buyers now treat software supply chain compliance as a procurement gate, not a nice to have. If you sell SaaS into finance, healthcare, or defense, you have felt it. Security questionnaires get longer. Contracts include remediation SLAs. Auditors want evidence, not promises.
SBOM by design is the boring, effective answer. You generate a Software Bill of Materials by default, enforce dependency rules in CI, and keep audit evidence ready.
What this article is and is not:
- It is a production ready approach for SaaS teams that ship weekly or daily
- It is not a one time SBOM export before a big deal closes
- It assumes regulated constraints like GDPR, HIPAA, and PCI DSS
Insight: An SBOM is only useful if it is current, tied to a build, and backed by enforcement. A stale SBOM is procurement theater.
You will get templates, checklists, and a concrete SBOM pipeline blueprint for modern CI. You can hand parts of it to security, platform, and product without rewriting it.
Who this is for
If you are a consulting engineering leader, you likely sit between three forces:
- Sales needs fast answers for enterprise security reviews
- Engineering needs to ship without adding manual gates
- Security needs controls that survive audits
The goal is simple: reduce supply chain risk while keeping release cadence intact.
_> Proof points that matter
What we can point to when buyers ask for maturity
Why SBOM by design matters
Supply chain incidents are rarely “one big hack.” They are small gaps that compound.
Common failure modes we see in SaaS delivery:
- A transitive dependency pulls in a vulnerable crypto library
- A build uses “latest” and you cannot reproduce what shipped
- A team patches fast, but cannot prove it to the customer
- Procurement asks for SaaS security evidence and you scramble
Key Stat: In our delivery work across 360+ projects since 2012, the teams that pass enterprise reviews fastest are the ones with repeatable evidence, not the ones with the longest policy docs.
You do not need perfect compliance on day one. You need a path from “we think” to “we can show.”
What procurement is really asking
Most questionnaires map to the same underlying questions:
- What is in the product, including open source and third party components?
- How do you prevent risky components from entering the build?
- How fast do you detect and fix known vulnerabilities?
- Can you prove any of the above with timestamps and artifacts?
If you answer those four, you will cover most of SOC 2 style requests, plus the supply chain parts of HIPAA and PCI DSS programs.
SBOM best practices checklist
_> What to implement before your next enterprise review
Per release SBOMs
One SBOM per shipped artifact. Not a single repo wide inventory that drifts.
Traceability fields
Commit SHA, build ID, artifact digest, and timestamp included in SBOM metadata.
Immutable storage
SBOMs and scan reports stored in an artifact repository with retention and access logs.
Policy as code
License allowlist and vulnerability thresholds versioned and reviewed like application code.
Expiring exceptions
Any override has an owner and expiry date. Expired exceptions block releases.
Evidence pack output
A repeatable bundle per release: SBOM, scan report, provenance, and SLA summary.
SBOM basics that hold up
An SBOM is an inventory of components in a software artifact. In SaaS, that usually means multiple artifacts:
- Backend services (containers, serverless packages)
- Frontend bundles
- Mobile apps, if you ship them
- Infrastructure as code modules, sometimes requested
SBOM best practices start with consistency. Same format. Same place. Same naming. Same linkage to a build.
Insight: Treat the SBOM like a test report. If it is not tied to a commit and build ID, it will not survive an audit.
Formats: what to pick
Two formats dominate enterprise conversations:
- SPDX: older, widely recognized, strong license metadata
- CycloneDX: popular in app security tooling, good for dependency and vulnerability workflows
If you have to pick one, pick the one your scanning and customer tooling can consume without friction. Many teams generate both.
| Format | Best at | Where it fits in SaaS | Watch outs |
|---|---|---|---|
| SPDX | License and attribution | Legal review, procurement packets | Can feel heavy if you only need vuln workflows |
| CycloneDX | Dependency and vuln pipelines | CI enforcement, security automation | License coverage depends on how you generate it |
A practical rule:
- CycloneDX for pipelines
- SPDX for legal and distribution
If that feels like duplication, measure it. If it adds less than 2 minutes to CI and saves hours in procurement, it is worth it.
Generation: when and where
Generate SBOMs at build time, not at merge time. You want the SBOM to represent what shipped.
Minimum viable generation points:
- On every container image build
- On every frontend build that produces a deployable artifact
- On every release tag, as a signed artifact
You also need identity:
- Commit SHA
- Build ID
- Artifact digest (for containers)
- Environment (prod staging) if customers ask for it
If your team uses GitHub Actions, GitLab CI, or CircleCI, this is straightforward. The hard part is governance and exceptions, not tooling.
Distribution: who gets it
You will distribute SBOMs in three ways:
- Internal: security and engineering use it for scanning and triage
- Customer on request: enterprise buyers, auditors, regulated clients
- Automated exchange: some customers will want SBOMs via a portal or ticket system
Keep distribution boring:
- Store SBOMs in an immutable artifact repository
- Provide a stable URL pattern per release
- Log access for audit trails
Do not email SBOMs around. It breaks traceability.
Policy template starter
Allowed licenses and risk thresholdsUse this as a first draft. Keep it short, enforce it in CI, then iterate. Allowed licenses (default allow)
- MIT
- Apache 2.0
- BSD 2 Clause, BSD 3 Clause
- ISC
Review required (legal and security)
- LGPL (any version)
- MPL 2.0
- SSPL
Blocked (default deny)
- GPL 3.0
- AGPL 3.0
Vulnerability thresholds (runtime dependencies)
- Block: critical
- Exception required: high (expires in 30 days)
- Track: medium (fix within 60 days)
Operational rules
- Exceptions must have owner, ticket, expiry
- Any exception that expires blocks the next release
- Policy changes require code review from security owner
Dependency governance that scales
SBOMs tell you what is there. Governance decides what is allowed to get there.
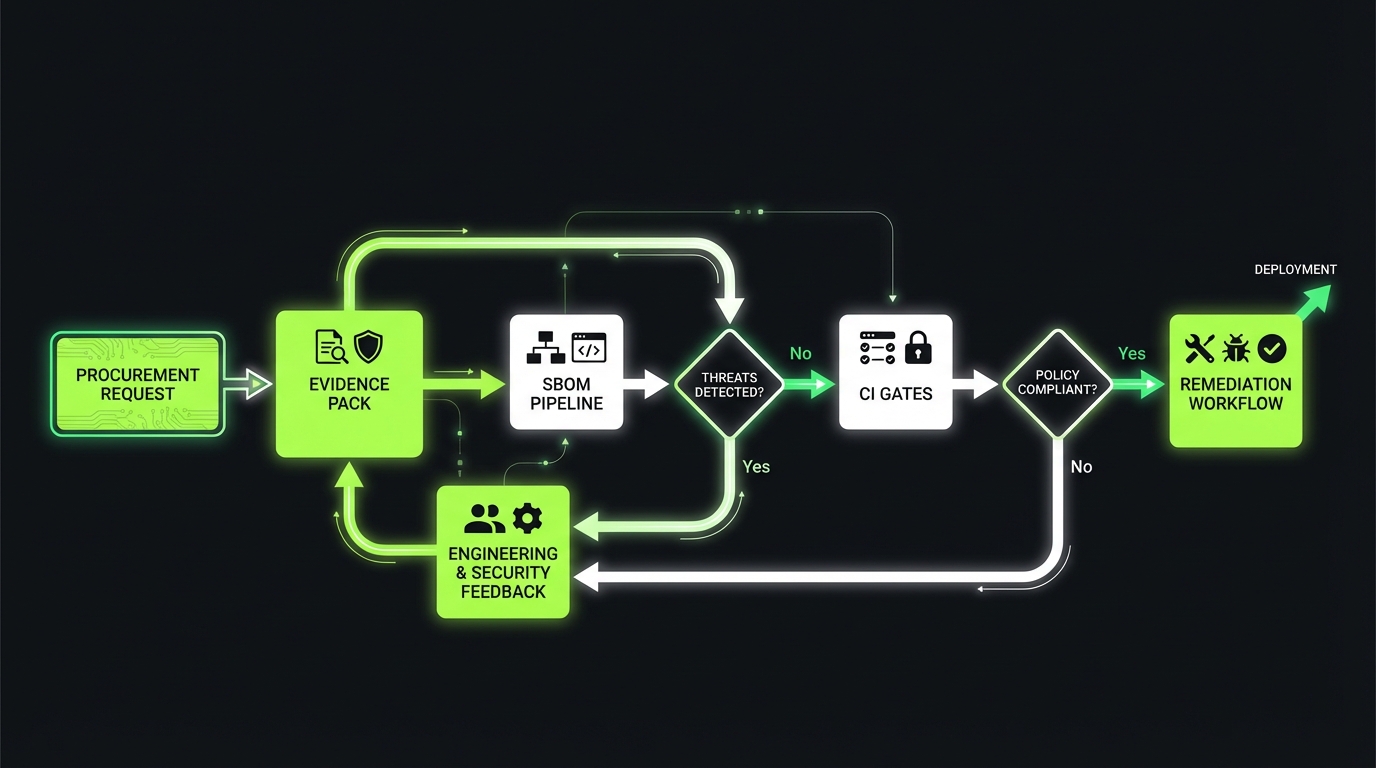
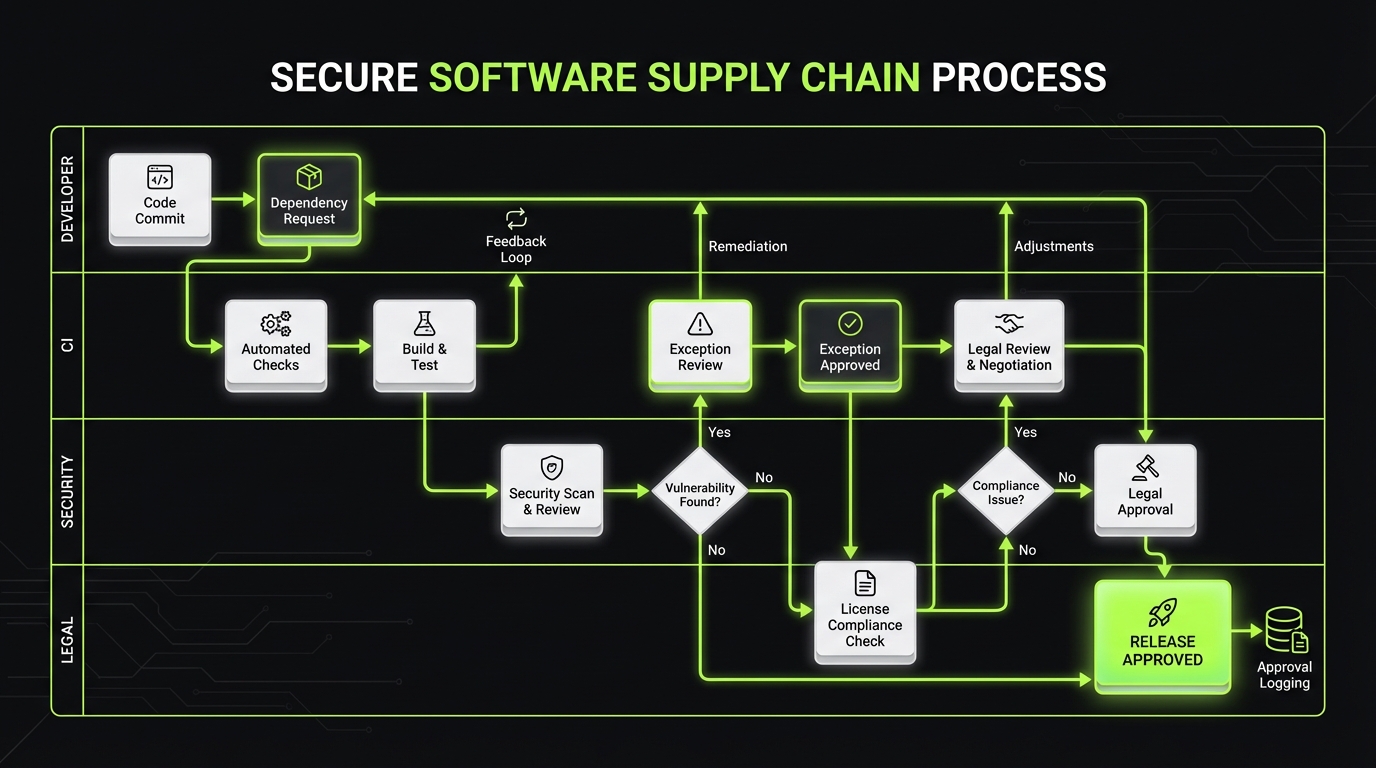
CI Gates With Evidence
Scan, block, publish artifactsUse CI as the control plane:
- Generate SBOM
- Scan SBOM and source dependencies (SCA + license)
- Gate on policy (for example: block critical runtime vulnerabilities)
- Allow expiring exceptions
- Publish evidence artifacts (SBOM, scan reports, signed outputs)
Based on delivery work across 360+ projects since 2012, teams pass enterprise reviews fastest when they can show repeatable evidence, not longer policy docs. Cycle time note: automation can replace manual security review for routine changes. Track pipeline duration and false positive rate so gates do not become a release tax.
Dependency governance is where most SaaS teams either overcorrect or under invest.
Overcorrect looks like:
- A central committee approves every package
- Engineers bypass controls to ship
- The policy exists, but CI does not enforce it
Under invest looks like:
- No pinning, lots of “latest”
- No owner for dependency updates
- No license policy until a deal is blocked
Insight: The best governance is opinionated automation plus a fast exception path.
Approvals: the minimum you need
You do not need to approve every dependency. You need to approve categories.
A practical model:
- Auto approved: common libraries with low risk profile and permissive licenses
- Review required: crypto, auth, networking, deserialization, build tooling
- Blocked: abandoned packages, unknown licenses, high severity known vulns
Make approvals visible:
- A dependency allowlist in version control
- Ownership tags per package group
- A ticket reference for exceptions
If you cannot explain why a package is allowed, it should not be allowed by default.
Pinning and updates: keep it reproducible
Pinning is not optional if you want audit quality SBOMs.
Rules that work in practice:
- Pin direct dependencies to exact versions
- Lock transitive dependencies via lockfiles
- Use deterministic builds where possible
- Record artifact digests in release notes
Then make updates routine:
- Weekly automated dependency update PRs
- A fixed review window (for example, 30 minutes twice a week)
- A rollback plan that is tested, not theoretical
Hypothesis to validate: track “dependency update lead time” and “vuln patch lead time.” If those grow, governance is slowing delivery.
SBOM pipeline blueprint
_> A minimal sequence that works in modern CI
→ Scroll to see all steps
CI enforcement: scanning, gating, exceptions
If you want software supply chain compliance without slowing releases, CI is the control plane.
Dependency Rules, Not Meetings
Automation with a fast exception path- SBOMs tell you what is installed. Governance decides what is allowed.
- Avoid the two common traps:
- Overcorrect: central approval for every package. Engineers bypass controls. CI does not enforce policy.
- Under invest: loose versioning (“latest”), no owner for updates, license policy starts only when a deal is blocked.
- A workable model: automated checks in CI plus an exception process with an owner, a written reason, and an expiration date.
What to measure: number of exceptions open past expiry; median time to approve a justified exception; % dependencies pinned to exact versions.
The pattern is consistent:
- Generate SBOM
- Scan SBOM and source dependencies
- Gate on policy
- Allow exceptions with expiration
- Publish evidence artifacts
Key Stat: In our SaaS work, the biggest cycle time wins come from removing manual security reviews for routine changes. Automation turns a 2 day wait into a 10 minute pipeline step.
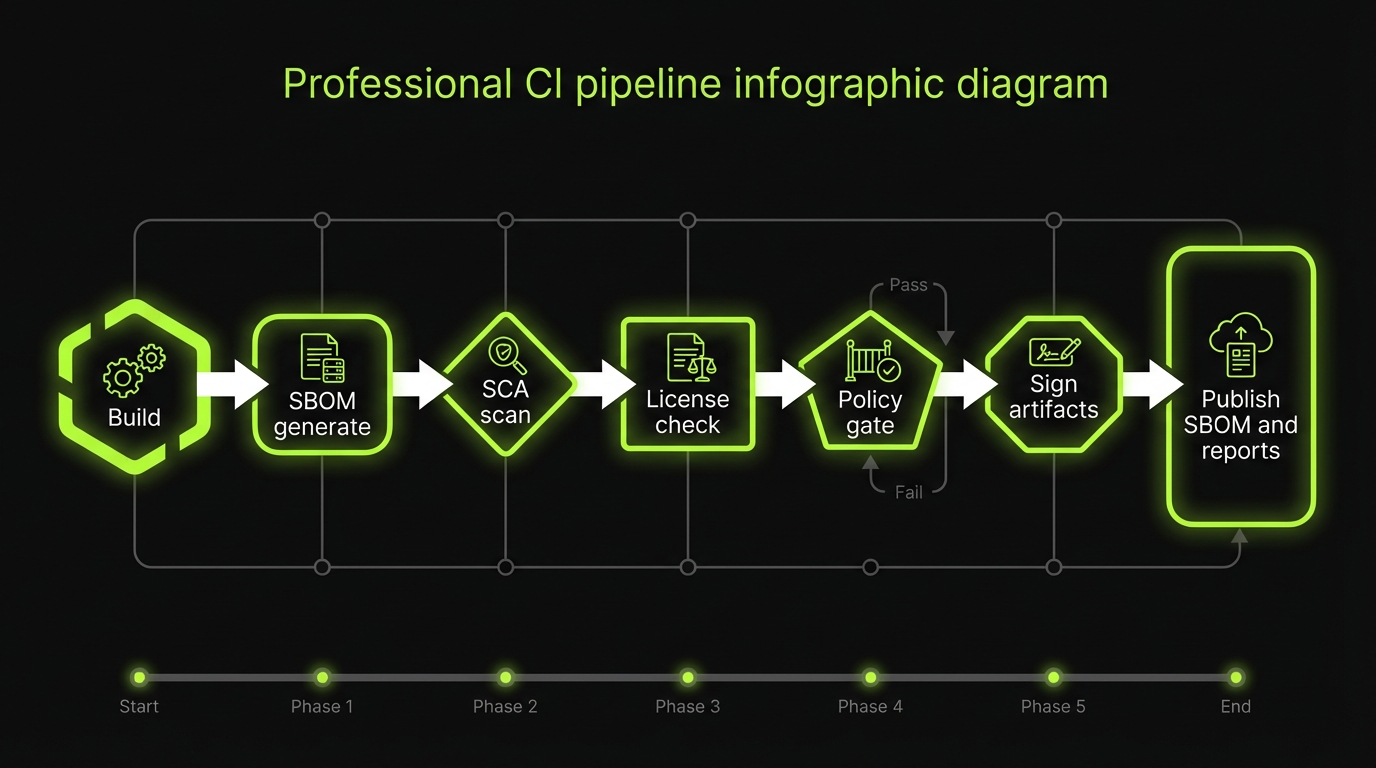
SBOM pipeline blueprint for modern CI
Here is a production ready SBOM pipeline blueprint. Adapt names to your stack, keep the sequence.
- Build artifact
- Container image, frontend bundle, or package
- Generate SBOM
- One SBOM per artifact, include commit and digest
- SCA scan
- Vulnerabilities, known exploited checks, dependency health signals
- License scan
- Match against allowed licenses policy
- Policy gate
- Block, warn, or require exception
- Sign and attest
- Sign artifact and SBOM, generate provenance
- Publish
- Store SBOM, scan report, and gate decision in artifact store
A simple gating model:
- Fail build on critical severity in runtime dependencies
- Warn on medium severity with an SLA clock
- Require exception for any blocked license
Example policy as code sketch:
policy:
vulnerabilities:
fail_on:
severity: ["critical"]
scope: ["runtime"]
warn_on:
severity: ["high"]
scope: ["runtime"]
licenses:
allowed:
- "MIT"
- "Apache-2.0"
- "BSD-3-Clause"
blocked:
- "GPL-3.0"
- "AGPL-3.0"
exceptions:
max_days: 30
require_ticket: true
require_owner: true
Keep it boring. The sophistication comes later, after you have baseline coverage.
Exceptions: make them safe
Exceptions will happen. A zero exception policy is not realistic.
Make exceptions measurable:
- Must include owner, reason, and ticket
- Must include expiration date
- Must include scope (service, dependency, version)
- Must trigger alerts before expiry
Anti pattern: “temporary exception” with no expiry that becomes permanent.
A good exception process reduces risk because it creates a paper trail and forces a decision.
This is the playbook we use when teams fear “security gates will kill velocity.”
- Start with one service and one gate
- Automate dependency updates on a schedule
- Make exceptions easy but temporary
- Publish one evidence pack per release
- Track two metrics: patch lead time and exception count
What usually slows teams down:
- Manual approvals for routine libraries
- No owner for dependency updates
- No agreed severity thresholds
What speeds teams up:
- Policy as code
- Deterministic builds
- A default exception workflow that is visible and expiring
What enterprise buyers get
_> Why this reduces procurement friction
Faster security reviews
You answer “what is in the product” and “how do you control it” with artifacts, not meetings.
Lower incident blast radius
When a CVE drops, you can locate affected services and versions quickly and patch with confidence.
Predictable remediation
Clear SLAs and evidence reduce escalations and contract risk during renewals.
Reproducible releases
Pinned dependencies and provenance make it possible to recreate what shipped, which helps during audits and incidents.
Disclosure, remediation, and audit evidence
SBOMs and CI gates reduce risk. They do not eliminate it. You still need a vulnerability disclosure and remediation system that can survive buyer scrutiny.
SBOMs That Survive Audits
Treat it like a test report- Generate the SBOM at build time, not “before the deal.” Store it next to the artifact it describes.
- Attach hard identifiers: commit SHA, build ID, artifact digest. Without this, you cannot prove what shipped.
- Standardize: one format, one naming scheme, one storage location. In audits, inconsistency looks like missing control.
Failure mode: a “current” SBOM that is not tied to a build becomes stale in days and turns into procurement theater. What to measure (hypothesis): % of production artifacts with an SBOM linked to a digest; time to produce an evidence pack for one release.
This is where SaaS security evidence matters most. It is the difference between “we are secure” and “we can prove our response time.”
Insight: Buyers do not expect zero vulnerabilities. They expect predictable detection, triage, and patch timelines.
Vulnerability disclosure and remediation SLAs
Define SLAs by severity and make them enforceable.
A common, defensible baseline:
- Critical: triage within 24 hours, fix or mitigate within 72 hours
- High: triage within 3 business days, fix within 14 days
- Medium: triage within 10 business days, fix within 30 to 60 days
- Low: fix as part of normal backlog
Two notes that prevent future pain:
- Define what counts as “mitigation” (feature flag off, WAF rule, dependency override)
- Define what “fix” means for SaaS (deployed to production, not merged)
If you cannot meet these today, do not fake it. Start with what you can meet and track improvement.
Audit evidence: what procurement will ask for
Procurement teams tend to ask for the same evidence bundle. Build it once.
Evidence categories:
- SBOMs per release, with timestamps and identifiers
- SCA scan reports and gating outcomes
- License policy and proof of enforcement
- Vulnerability management process and SLA metrics
- Incident response runbooks and post incident summaries when relevant
- Access controls, logging, and change management evidence
Here is a quick mapping table you can use internally:
| Buyer question | Evidence to show | Where it should live |
|---|---|---|
| What components are in the product? | SBOM for the shipped artifact | Artifact repository, release bundle |
| How do you prevent risky deps? | CI policy gate logs, allowlist, exception tickets | CI logs, repo, ticketing system |
| How fast do you patch? | SLA policy, time to remediate metrics, release notes | Security dashboard, reports |
| How do you handle disclosures? | Security.txt, intake workflow, comms template | Public page, ticket system |
| Can you reproduce a release? | Build provenance, signed artifacts, digests | CI, artifact store |
Example: In regulated delivery work, the fastest path through procurement was a single “evidence pack” folder per release: SBOM, scan report, gate decision, and provenance. No hunting across tools.
Conclusion
SBOM by design is not a compliance checkbox. It is an operating model.
If you want software supply chain compliance that does not slow releases, focus on these moves:
- Generate SBOMs at build time and tie them to commits and artifact digests
- Govern dependencies with automation, not meetings
- Enforce policy in CI with clear gates and expiring exceptions
- Publish remediation SLAs you can meet and measure
- Prepare an evidence pack that procurement can validate in minutes
A practical next sprint plan:
- Pick one service that ships often
- Add SBOM generation and store artifacts per build
- Add one gate: block critical runtime vulnerabilities
- Add one policy: blocked licenses list
- Add one metric: time to remediate critical issues
Ship that. Then expand service by service.
Insight: Compliance by design is how you keep velocity. You do the work once, then let the pipeline enforce it forever.
Where Apptension fits in
When we build SaaS systems, including our own product Teamdeck, we treat supply chain controls as part of delivery flow, not a separate security project. In practice that means:
- Senior, self directed teams that can implement CI enforcement without stalling product work
- Evidence oriented delivery so enterprise buyers get SaaS security evidence on request
- Fast onboarding when a deal or audit creates a hard deadline
If you already have a platform team, this work is a force multiplier. We help you design the pipeline, implement the first services, and leave your team with maintainable policy as code.